Welcome to the PowerDNS Blog
PowerDNS Authoritative Server 5.1.1 Released
Peter van Dijk on Jun 08, 2026
Despite our best efforts, a severe bug escaped our testing while working on the 5.1.0 release. Users of the LMDB backend, when not using the new ``lmdb-split-domain-table'', would fail to update their last notifi...
PowerDNS Authoritative Server 5.1.0 Released
Peter van Dijk on Jun 03, 2026
Being out of excuses to postpone this release, we are releasing PowerDNS Authoritative Server version 5.1.0 today. A detailed list of changes can be found in the changelog. There are too many changes and bugfixes...

PowerDNS Recursor 5.2.10, 5.3.7 and 5.4.2 Released
Otto Moerbeek on Jun 03, 2026
Today we have released PowerDNS Recursor 5.2.10, 5.3.7 and 5.4.2. These releases are maintenance releases that fix a few bugs and have a few improvements. The most important ones are:
PowerDNS DNSdist 2.1.0 Release Candidate 1 Released
Remi Gacogne on Jun 02, 2026
Today we released the first release candidate for PowerDNS DNSdist 2.1.0. This new version brings a lot of bug fixes since the second beta, including security issues that have been recently fixed in stable branch...
PowerDNS DNSdist 2.0.6 Released
Remi Gacogne on May 21, 2026
Today we released DNSdist 2.0.6, fixing several issues. The notable ones are: the feature that was introduced in 2.0.0 to limit the rate of new TCP or QUIC connections that a given client can open per second has ...
PowerDNS Security Advisory 2026-06 for PowerDNS Authoritative Server
Peter van Dijk on May 20, 2026
Today, we are releasing two new versions of the PowerDNS Authoritative Server. These 4.9.15 and 5.0.5 versions provide fixes for the following PowerDNS Security Advisory: PowerDNS Security Advisory 2026-06: Multi...
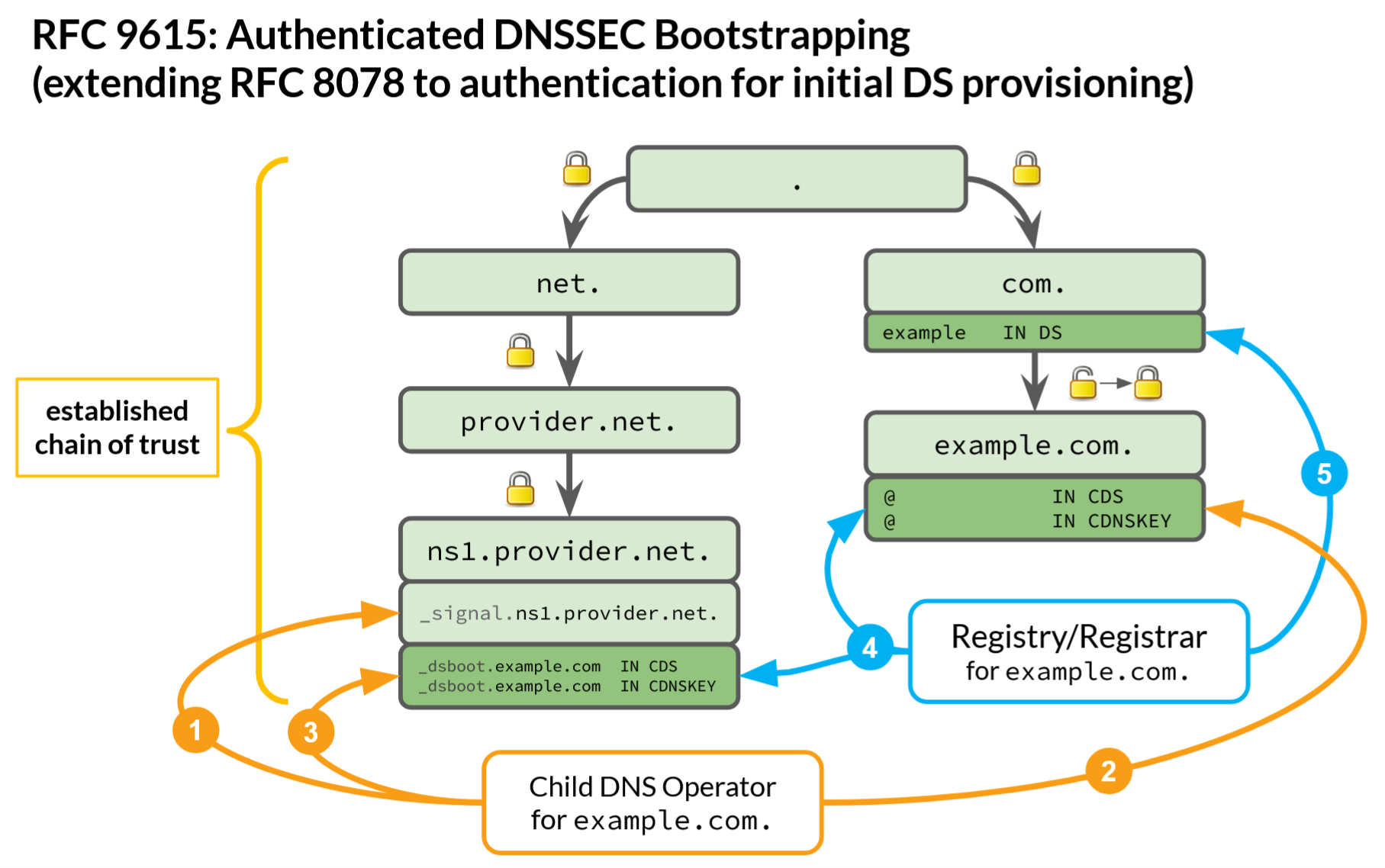
Automatic authenticated DNSSEC Bootstrapping in PowerDNS Authoritative
Peter van Dijk on May 12, 2026
The chain of trust is better off without leaps of faith: Automatic authenticated DNSSEC Bootstrapping in PowerDNS Authoritative Server Authors: Barbara Jantzen & Peter Thomassen (both from deSEC)
PowerDNS Authoritative Server 5.1.0-beta1 Released
Peter van Dijk on May 07, 2026
On this lovely day, we are releasing version 5.1.0-beta1 of the PowerDNS Authoritative Server. It contains many small new features and improvements over the previous 5.1.0-alpha1 release, as well as the unavoidab...
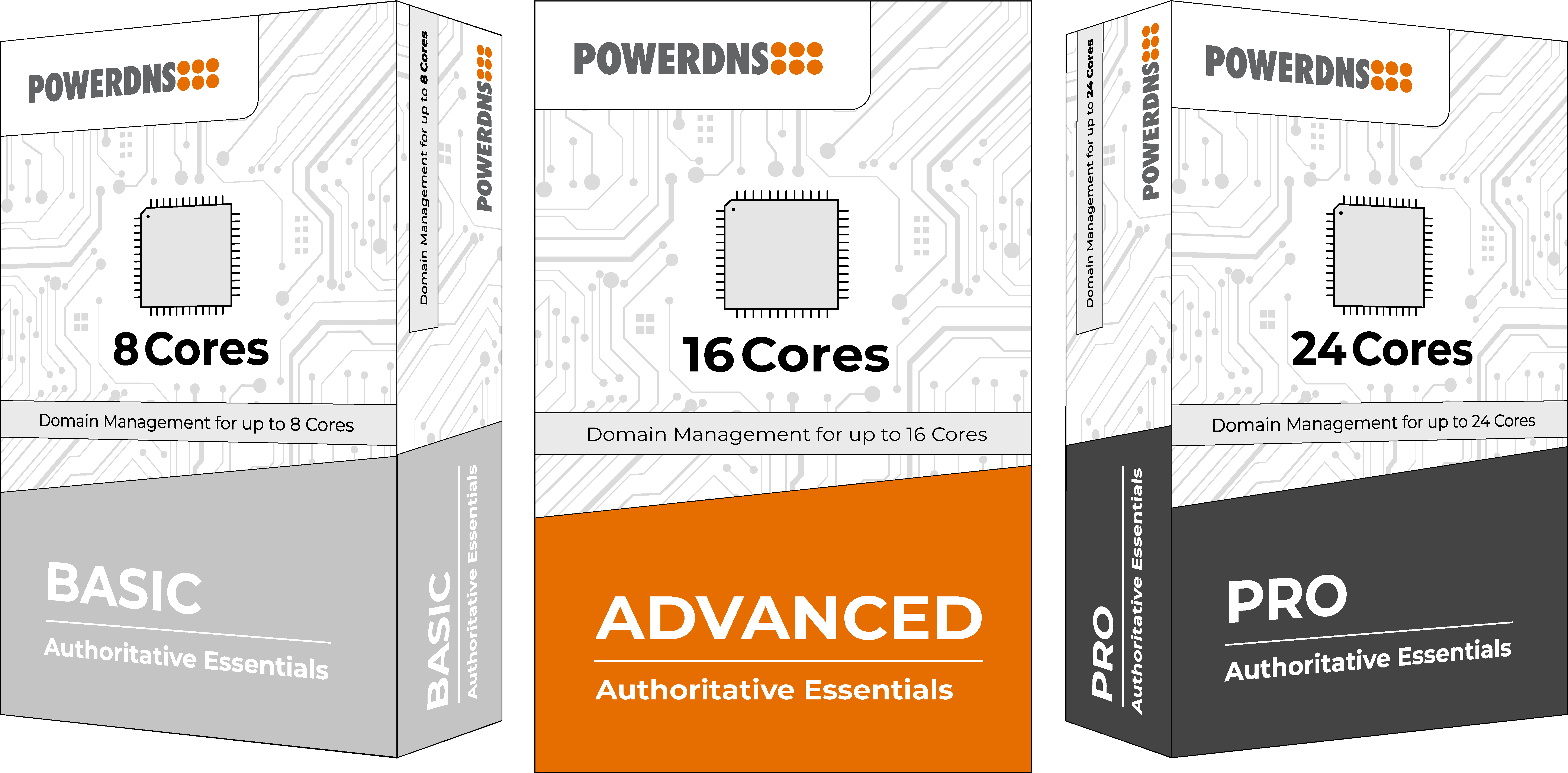
Introducing PowerDNS Authoritative Essentials
Oliver Michler on May 05, 2026
We’re thrilled to announce the launch of PowerDNS Authoritative Essentials – a streamlined, enterprise-grade solution designed for organizations that require high-performance, secure, and dependable DNS for their...
PowerDNS DNSdist 1.9.14 and 2.0.5 Released
Remi Gacogne on Apr 23, 2026
Today we again released two new versions of DNSdist, 1.9.14 and 2.0.5, fixing one regression introduced in 1.9.13 and 2.0.4, and several small issues that were not included in yesterday's security releases. The r...
